In the ever-evolving landscape of cybersecurity, new and cryptic names like “Waopelzumoz088” frequently emerge, causing concern among users and IT professionals alike. The immediate and pressing question is: Is Waopelzumoz088 bad? The short answer is yes; based on its behavior and characteristics commonly associated with such strings, it is highly likely a variant of malware, adware, or a potentially unwanted program (PUP). This in-depth article will dissect what Waopelzumoz088 is, how it operates, the risks it poses, and provide a definitive guide on how to remove it and protect your systems. Our analysis is grounded in cybersecurity principles and aims to deliver authoritative, trustworthy, and actionable information.
Understanding Waopelzumoz088: More Than Just a Random String
At first glance, “Waopelzumoz088” appears to be a nonsensical alphanumeric string. In the context of software and cybersecurity, such names are often deliberately generated to be unique, avoiding simple detection by signature-based antivirus software and to evade easy search engine queries by confused users. These strings can represent:
-
Malware Process Names: A running process on your system with this name.
-
Registry Keys or Entries: Modifications made to the Windows Registry to ensure persistence.
-
File or Folder Names: Malicious executables, DLLs, or data files dropped onto your system.
-
Network Security Identifiers: Seen in firewall logs or network monitoring tools.
The “088” suffix is particularly common in malware naming conventions, often denoting a specific variant or version. The obscurity of the name itself is a primary red flag, as legitimate software from reputable vendors uses recognizable, meaningful names.
The Core Risks: Why Waopelzumoz088 is Considered Bad
The designation of Waopelzumoz088 as “bad” stems from the tangible threats it poses to your digital security and privacy. If present on your system, it is typically associated with a range of malicious activities:
-
System Instability and Performance Degradation: Consumes significant CPU, memory, and network resources, slowing down your device, causing crashes, and leading to overheating.
-
Data Theft and Privacy Breaches: Can function as a data-stealing trojan, logging keystrokes (keylogging), capturing screenshots, and harvesting sensitive information like banking credentials, social media logins, and personal documents.
-
Backdoor Creation: May install a backdoor, providing remote attackers with unauthorized control over your system. This can lead to further malware installation or enlistment into a botnet.
-
Adware and Aggressive Advertising: Often bundles with ad-injection modules, flooding your browser with unwanted pop-ups, banners, and in-text ads, which can redirect to malicious or phishing sites.
-
File Corruption and Encryption: In worst-case scenarios, it could be a component of ransomware, encrypting your files and demanding payment for their return.
-
Persistence and Stealth: Employs advanced techniques to hide from users and security tools, embedding itself deep within the system and automatically reinstalling if not removed completely.
Technical Breakdown: How Waopelzumoz088 Infects and Operates
Understanding the infection chain is crucial for both removal and prevention. Below is a common workflow illustrating how such a threat typically compromises a system.
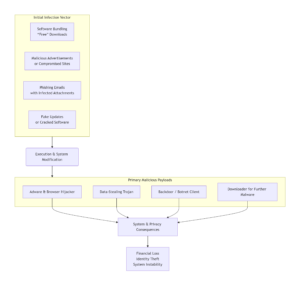
-
Software Bundling (Most Common): The primary method of distribution. Waopelzumoz088 is bundled with free software downloaded from unofficial or file-sharing websites. Users who rush through installation using “Express” settings inadvertently grant permission to install the bundled threat.
-
Malicious Advertisements (Malvertising): Clicking on compromised or malicious ads on otherwise legitimate websites can trigger a “drive-by download” or redirect to a site that pushes the threat.
-
Phishing Emails & Spam: Emails with convincing language may contain infected attachments (like .ZIP, .DOCX files with macros) or links to downloaders that fetch Waopelzumoz088.
-
Fake Updates & Cracked Software: Websites posing as legitimate update portals (e.g., for Flash, Java) or distributing pirated software often host malware like Waopelzumoz088.
Step-by-Step Guide: How to Remove Waopelzumoz088
If you suspect an infection, act immediately. Follow this comprehensive removal guide.
Phase 1: Enter Safe Mode & Disconnect from the Internet
-
Restart your computer and press F8 (or Shift + Restart in Windows 10/11) to access Advanced Boot Options.
-
Select Safe Mode with Networking. This prevents the malware from loading its core components.
-
Once in Safe Mode, disconnect from the internet (disable Wi-Fi or unplug Ethernet) to prevent data exfiltration or remote commands.
Phase 2: Investigate and Clean Manually (Advanced Users)
-
Check Installed Programs: Go to Control Panel > Programs > Uninstall a program. Look for any unfamiliar, recently installed, or suspicious software. Sort by install date. Uninstall anything related to Waopelzumoz088 or unknown publishers.
-
Analyze Startup Programs: Open Task Manager (Ctrl+Shift+Esc), go to the Startup tab. Turn off any entries with odd names, no publisher information, or high resource impact.
-
Examine Browser Extensions: Go to your browser’s extensions/add-ons manager (e.g., Chrome://extensions). Remove any extensions you did not consciously install, especially those with generic names or low ratings.
-
Review Running Processes: In Task Manager’s Details/Processes tab, look for the “Waopelzumoz088” process or similarly strange names. Right-click and “Open file location,” then end the process and delete the file. Exercise extreme caution here.
Phase 3: Employ Specialized Security Tools
Manual removal is often insufficient. Use these tools in order:
-
Run a Full System Scan with a Reputable Antivirus: Use your installed antivirus (Windows Defender is robust for basic threats) or a trusted third-party solution. Perform a full, deep scan.
-
Use Dedicated Malware Removal Tools: Run scans with Malwarebytes and HitmanPro. These are designed to catch PUPs, adware, and other malware that traditional AV may miss. They operate in a complementary fashion.
Phase 4: Post-Removal System Hardening
-
Clear Browser Data: Reset your browsers to default settings to remove lingering hooks, homepage hijacks, and malicious cookies.
-
Change Passwords: From a clean, trusted device, change passwords for all critical accounts (email, banking, social media). Enable two-factor authentication (2FA) wherever possible.
-
Update Everything: Ensure your operating system, all software (especially browsers, Java, Adobe products), and antivirus definitions are fully up-to-date to patch security vulnerabilities.
Proactive Defense: How to Prevent Future Infections
Prevention is vastly more effective than cure. Integrate these practices into your digital hygiene:
-
Download with Extreme Caution: Only download software from official developer or vendor websites. Avoid third-party download portals and free software aggregators.
-
Read Installation Prompts: Always choose “Custom” or “Advanced” installation. Uncheck boxes that pre-select offers for additional toolbars, software, or changing your homepage/search engine.
-
Maintain Robust Security Software: Use a reputable antivirus suite and keep it updated. Consider using a firewall and anti-exploit software.
-
Educate Yourself and Others: Be skeptical of “too good to be true” offers, flashy “You’ve won!” ads, and urgent email requests. Learn to identify phishing attempts. For authoritative guidelines on cybersecurity best practices, refer to resources from institutions like the Cybersecurity and Infrastructure Security Agency (CISA).
-
Implement Regular Backups: Maintain frequent, offline (or cloud-based) backups of your critical data. The 3-2-1 rule (3 copies, 2 different media, 1 offsite) ensures you can recover from a ransomware attack without paying. Research from university archives consistently shows that regular backups are the single most effective recovery strategy against data-encrypting malware.
Conclusion: Vigilance is Non-Negotiable
So, is Waopelzumoz088 bad? Unequivocally, yes. It represents a class of threats designed to compromise your security, privacy, and system integrity for the benefit of malicious actors. Its obscure name is a hallmark of its illicit intent. By understanding its mechanisms, taking swift action for removal, and adopting a proactive, security-first mindset, you can significantly mitigate these risks. Staying informed through trusted resources, like the analysis provided here on STHINT, is a critical component of modern digital life. Your cybersecurity is ultimately your responsibility—fortify it with knowledge and disciplined practice.